AI Summarized Hacker News
Front-page articles summarized hourly.
Could not summarize article.
HN Comments
Omniglot is an online encyclopedia of writing systems and languages. It surveys scripts (alphabets, abjads, abugidas, syllabaries, constructed scripts) and natural and constructed languages, with sections on language learning tips, phrases, numbers, colors, idioms, and multilingual pages. The site also features news, blogs, quizzes, and an extensive directory of languages and resources, including examples like Manjak, Vute, Lotha, and Flāmtón. © 1998–2026 Simon Ager.
HN Comments

Zed argues collaboration should happen in code as it evolves, not after commits. They unveil DeltaDB, a version control that records every operation as a delta, so code, conversations, and edits stay linked. Deltas enable addressing code over time, allow conflict-free replicated worktrees for concurrent edits by people and agents, and let conversations accompany code. The goal: you shouldn’t need to commit to collaborate. Git/CI stay for checks, while DeltaDB handles collaboration. A beta is coming soon; join the waitlist.
HN Comments
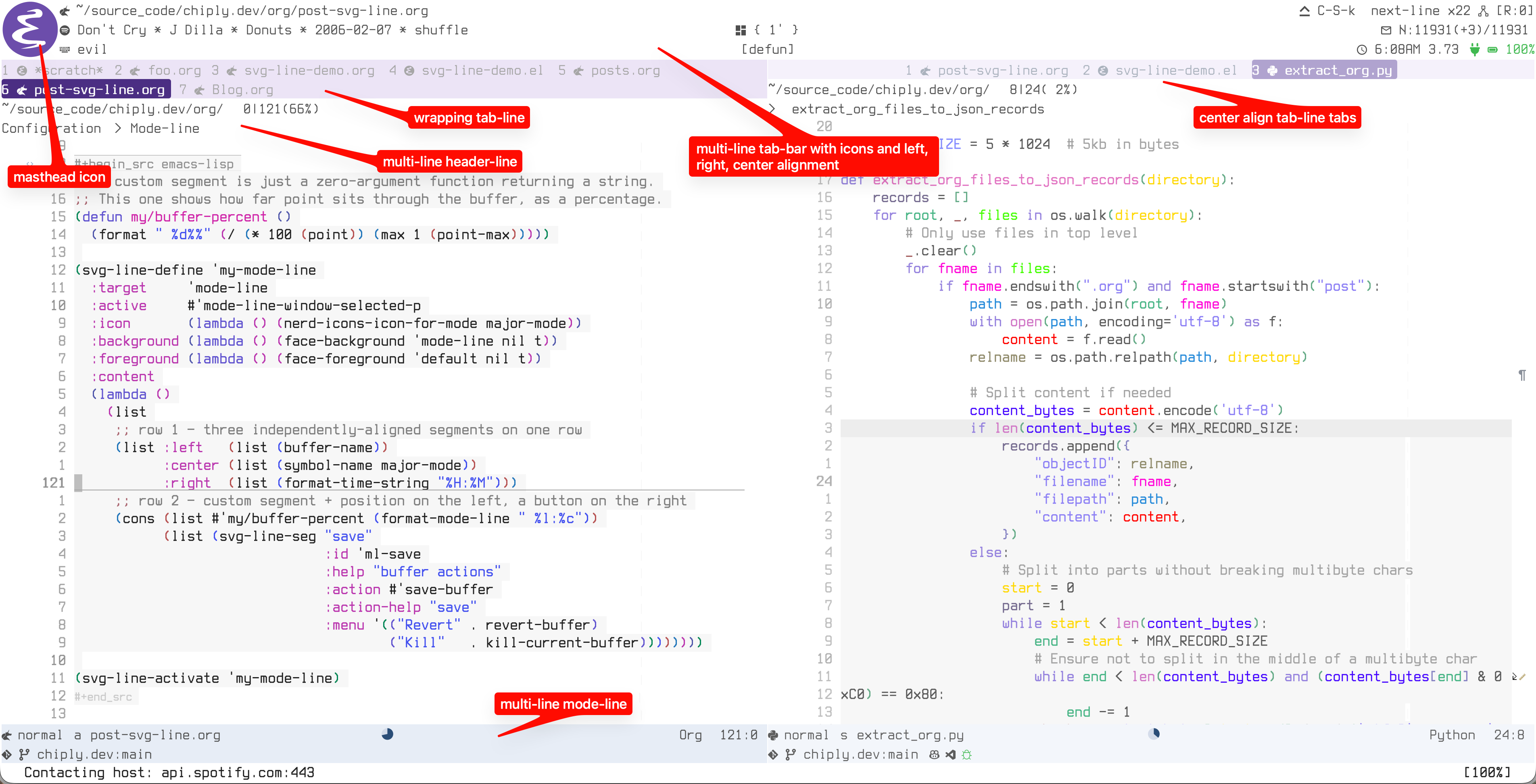
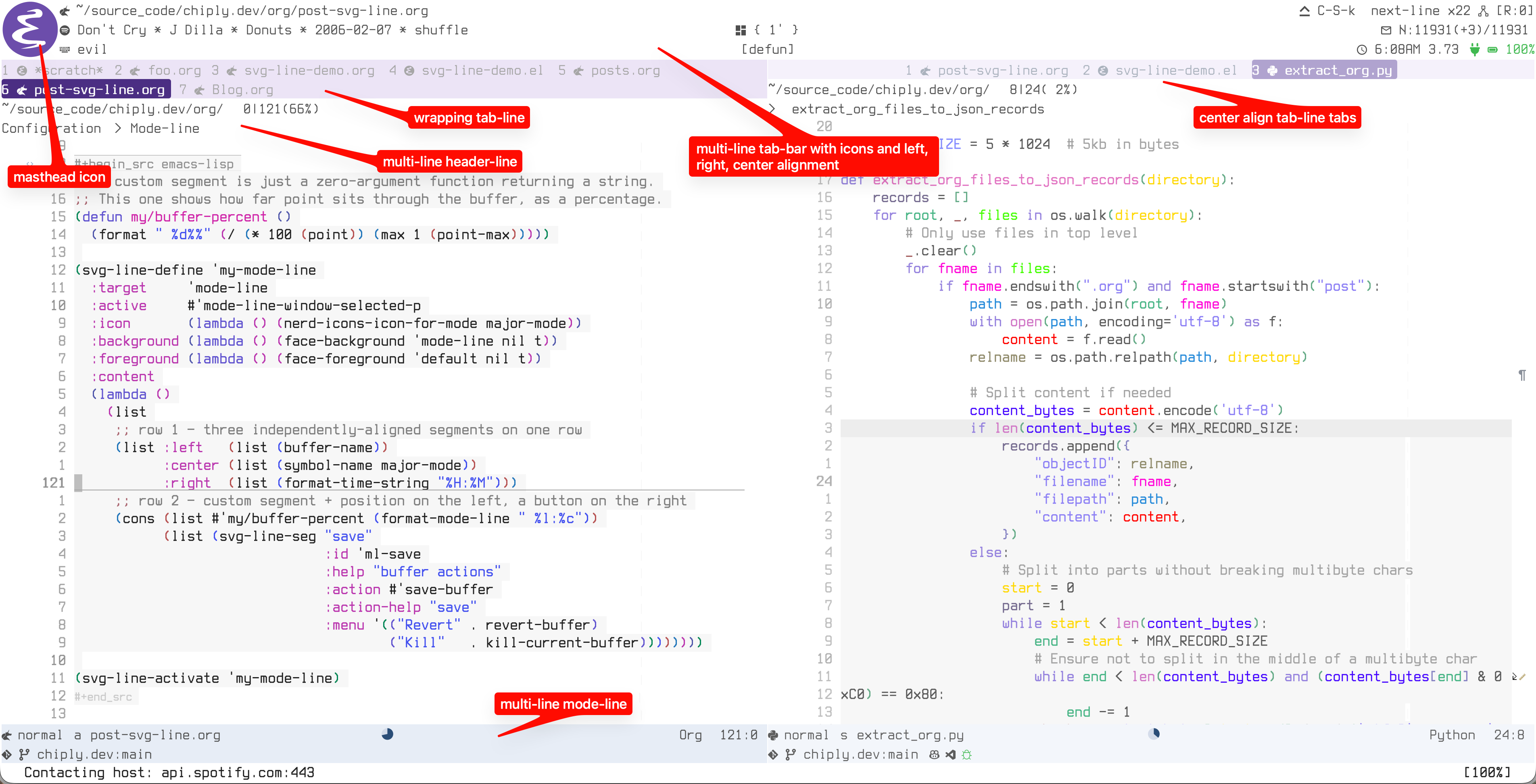
svg-line is an Emacs package that renders all four status bars (mode-line, header-line, tab-bar, tab-line) as unified SVG images, giving consistent multi-line layouts, alignment, icons, and interactivity across bars. It uses Emacs SVG rendering, with a simple config: define a :content function and call svg-line-activate. Features include multi-line rows on every bar, wrap-enabled tab-line, clickable segments, text-icon glyphs, masthead icons, dynamic indicators, and scale-aware rendering. SVGs enable precise placement, mouse events, and uniform configuration. Mode-line examples show simple and rich setups; tab-line supports wrapping. Acknowledge Nicolas Rougier.
HN Comments
In May, solar topped coal for the first time in the US, supplying 12.8% of electricity versus coal’s 12.2%. Solar became the third-largest source after natural gas and nuclear, with coal at a monthly low in April. Despite Trump’s push for coal, solar and storage accounted for 91% of new generating capacity in Q1, making solar the leading source of new power for five years. Globally, renewables are growing, with the IEA forecasting about 45% of electricity from renewables by 2030.
HN Comments
Security blogger MrBruh discovered a remote code execution in AMD’s AutoUpdate: update URLs were HTTP with no signature checks, enabling MITM tampering. AMD initially deemed the issue out of scope for their bug bounty and asked for a post to be taken down. After community pressure, AMD reviewed it, issued a CVE, and patched the flaw by moving updates to the application layer and enforcing HTTPS, though CRC-32 is the only check (not cryptographic). A separate redirection bug could crash the updater. The author recommends uninstalling old tools and updating from AMD’s site.
HN Comments
An e-petition to the House of Commons opposes Bill C-22 (lawful access). It calls to withdraw the bill, remove any suspicionless bulk metadata retention, and bar future measures that weaken encryption. The petition argues C-22 would allow up to one year of metadata collection and mandate interception capabilities, creating cybersecurity risks, and invites Canadians to sign, with privacy and accessibility notices included.
HN Comments

Anthropic apologizes for invisible guardrails on Claude Fable 5 that quietly throttled distillation and hindered researchers and rivals. It will make those safeguards visible and, when triggered, have Fable fall back to Claude Opus 4.8 with a prominent user notice: “You will see this every time it happens.” The policy change aligns with broader safety rules and treats high-risk areas like biology similarly. The move follows backlash over invisible restrictions and aims to balance rapid AI development with transparency and accountability.
HN Comments
Could not summarize article.
HN Comments

Euro-Office, the open-source web office built with Nextcloud and Ionos, has released its first stable version. It enables collaborative editing of documents, spreadsheets, and presentations and aims to reduce dependence on Microsoft Office and Google Docs. The release focuses on code cleanup, security updates, and integration into existing tools; desktop/mobile apps and full ODF support are planned for the next versions. It will be offered as an office module within partner ecosystems (Nextcloud, Ionos, XWiki, OpenProject, etc.), with future options between Collabora and Euro-Office. Docker and GitHub tests are available; licensing dispute with OnlyOffice has been resolved.
HN Comments
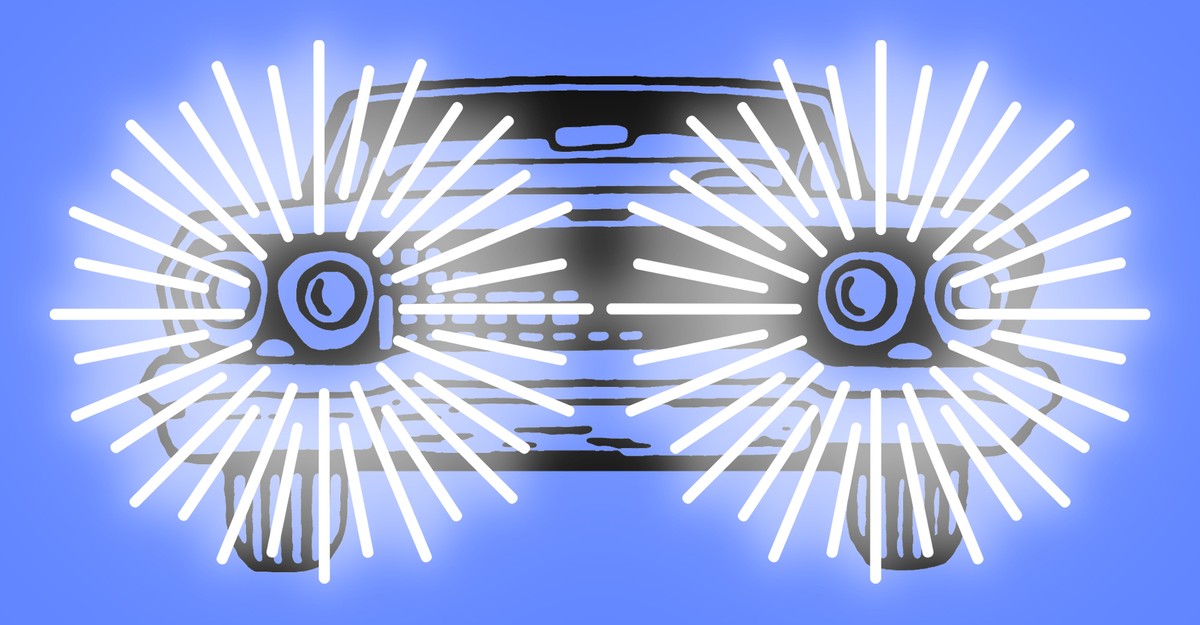
America’s headlights are blinding due to bright LED beams on tall vehicles. Adaptive driving beam (ADB) could dim glare, but U.S. rules haven’t adopted the international standard; NHTSA’s 2021 update kept a separate binary high/low-beam system. Only a few models (Rivian 2024, Tesla Model Y, upcoming Audi Q9) use compliant ADB after major redesigns. Replacing older cars will take years (avg 13-year life), so glare persists. Wider regulatory alignment could let manufacturers enable safer adaptive beams via OTA updates.
HN Comments

Talos is a scalable, secure API key server that issues, verifies, revokes, and derives API keys and short-lived tokens (JWTs and macaroons) for users, services, machines, and AI agents. It supports low-latency, scalable verification with caching and offline derivation. Deploy self-hosted or on the Ory Network; OSS (SQLite) or Enterprise (multi-node, multi-tenancy, SLAs). It integrates with the Ory stack (Kratos, Hydra, Oathkeeper, Keto) and emphasizes strong security (constant-time ops, centralized routing, tenant isolation).
HN Comments

IEEE Spectrum argues orbital data centers face prohibitive thermodynamic and economic hurdles, making space compute viable only for niche tasks. In vacuum, cooling must be radiative, requiring vast radiator areas per watt (a 32-GPU rack could need ~80 m^2). A 100 MW center would need thousands. Radiation degrades radiators and chips, raising area ~40% over time; rad-hard hardware lags in performance. Solar power helps, but launch, shielding, redundancy, and mass penalties erase most savings. Today, use cases include Earth-observation data pre-processing and onboard collision avoidance; scalable space data centers need advanced radiators and autonomous servicing.
HN Comments
Queues are not a universal fix for overload. overload hits a bottleneck (DB, API, disk, CPU, I/O) that slows input, creating harmful back-pressure. People add queues to buffer, but queues often mask failures, risk data loss, and complicate maintenance. The solution is to identify the bottleneck and choose: back-pressure (limit input) or load-shedding (drop or degrade data). Build end-to-end, idempotent APIs with clear semantics and observability. Avoid using queues as a cure-all; use them only when appropriate and designed around system limits.
HN Comments

FPS.cob is a COBOL-based, retro-style first-person shooter prototype. It supports two map styles: map/level1.map (grid Wolf3D-like) and map/doom_sectors.map (DOOM-like with doors and varying heights). Build requires cobc, ffplay, and bash. From the repo root, run bash build.sh to compile and load a map (e.g., bash build.sh ./map/level1.map). Controls: W/S to move, A/D to turn, Space to fire, Q to quit. Assets in res/, maps in map/. License: Apache-2.0.
HN Comments
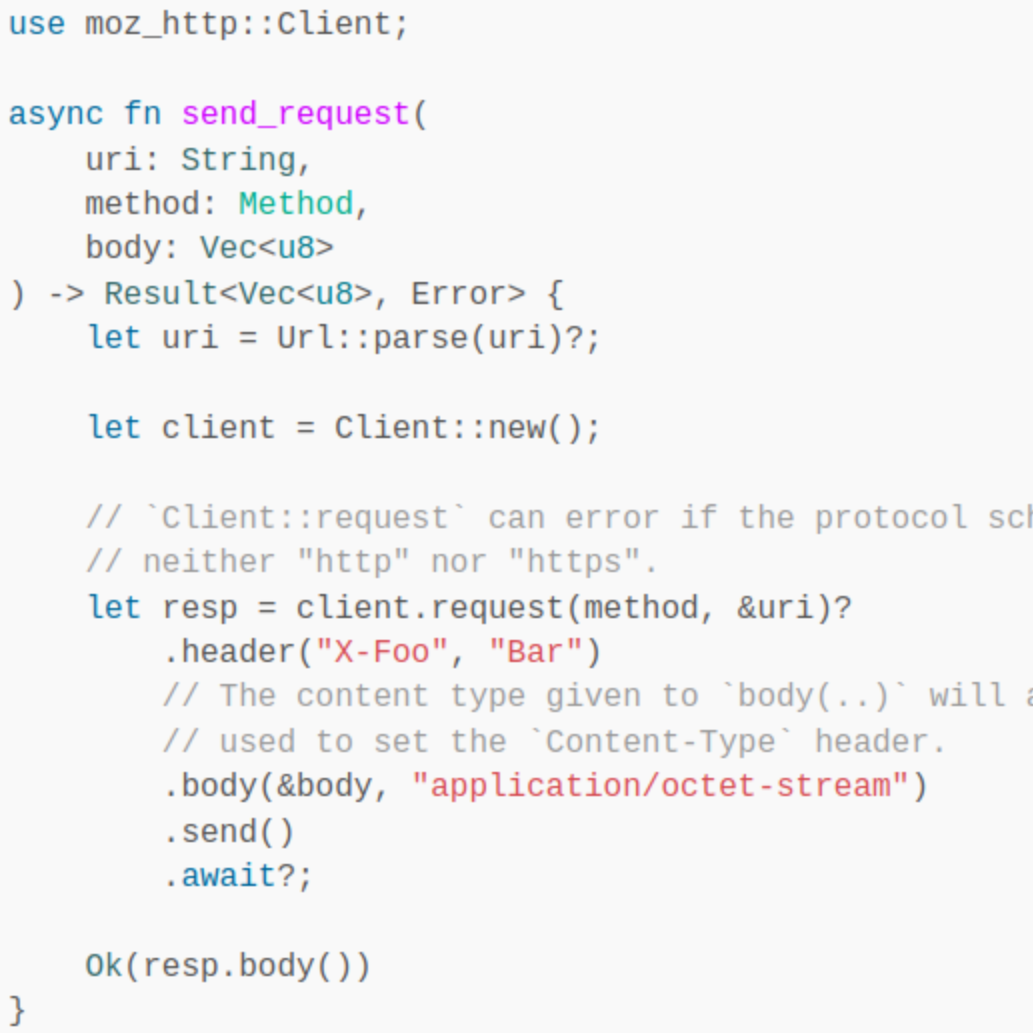
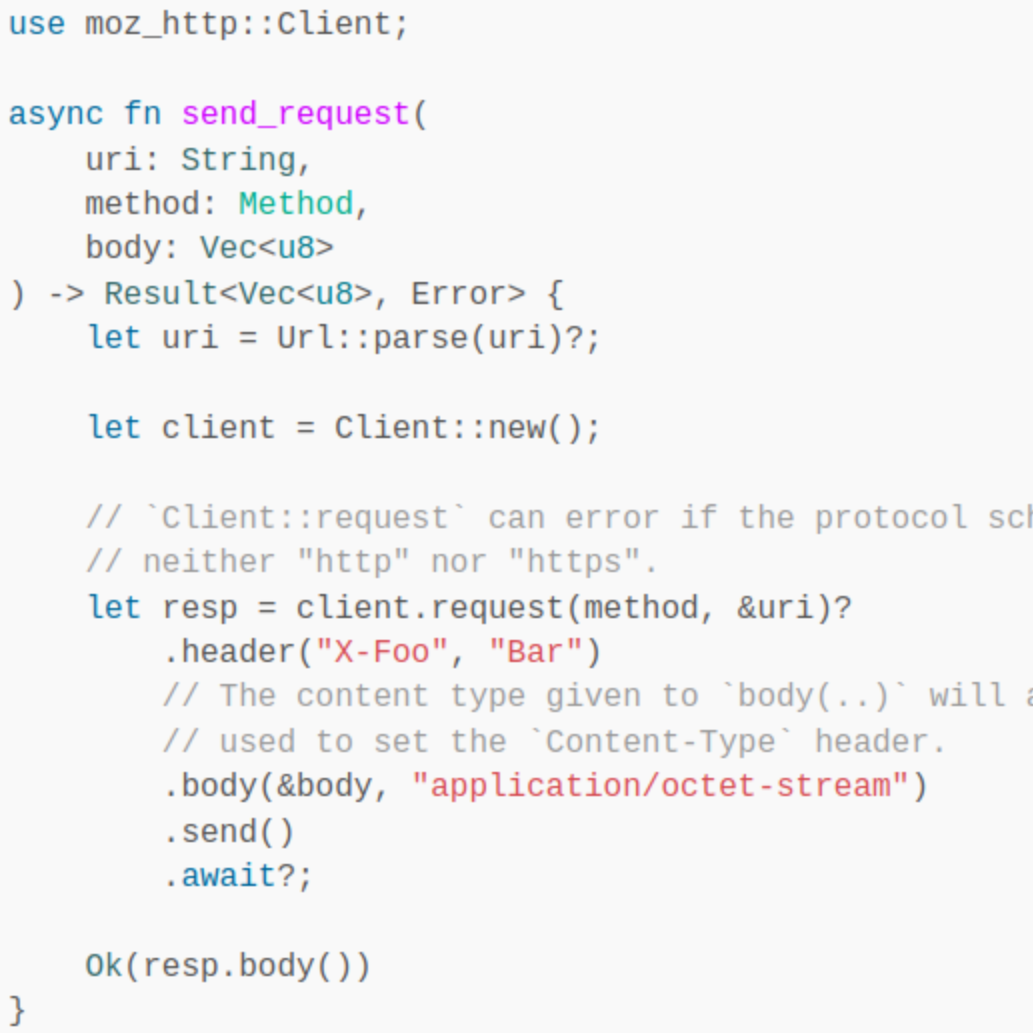
Brendan Abolivier’s second post details Thunderbird's Rust-based EWS protocol client for Microsoft Exchange, built with a C++ glue layer via XPIDL. It covers the fundamentals: asynchronous Rust using Mozilla’s XPCOM/Necko, an nsIChannel adapter (BufferingStreamListener, AsyncChannelOpener), and a safe HTTP client (moz_http::Client). It explains XML handling with quick-xml and a custom xml_struct serializer for EWS requests, plus the project’s cross-language architecture, shared utilities, and documentation gains from deep code archaeology. The feature shipped in Thunderbird 145, with plans to switch to Microsoft Graph and extend to calendar/address book.
HN Comments
Could not summarize article.
HN Comments

Open R1 is a Hugging Face project that fully open reproduces DeepSeek-R1. It provides scripts and Makefiles to train OpenR1 models via supervised fine-tuning (SFT), group-relative policy optimization (GRPO), and data generation, following a three-step plan: distill high-quality data, replicate RL (R1-Zero), and multi-stage RL. The repo includes datasets (Mixture-of-Thoughts, CodeForces-CoTs, OpenR1-Math-220k), instructions for setting up CUDA 12.4, vLLM/FlashAttention, and multi-node training, evaluation (LightEval), and data decontamination. Updates include released datasets and completed steps (May 2025).
HN Comments

Historic Haskell Free Library and Opera House, built in 1904 to straddle the Canada–US border, has opened a Canada-only entrance after US access rules barred Canadians from the original main entrance in Vermont. For a century people could move freely through the building; tighter rules effectively closed the shared entrance in Oct 2025. The Canada-side entrance, carved from a former emergency exit, was costly and partly funded by community fundraising.
HN Comments

Nextcloud Hub 26 Spring celebrates 10 years with a refined UI and more tool choice. It introduces Euro-Office alongside Collabora Online as default office suites, plus updates across apps: Collabora Online gains an AI chat sidebar, a customizable status bar, improved presentations, and smoother spreadsheets; Euro-Office emphasizes sovereignty and MS compatibility with offline text editing. Collectives search and Tables receive enhancements; Deck adds Gantt-style views and card dependencies; Talk adds private replies, Voice Rooms, and multi-account desktop; Mail/Calendar delegation; Assistant improvements; API updates; governance/compliance tools; ISV program and developer relations; webinar on June 18.
HN Comments
Made by Johno Whitaker using FastHTML